Researchers Find Way To Sneak Malicious Apps Through iOS App Store
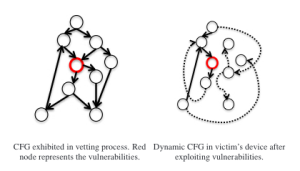
On the left is the Jekyll app’s control flow graph as Apple would have seen it during the screening process. On the right is how it would look after being remotely exploited.
The researchers, who appropriately dubbed their project “Jekyll,” created an app that would pass muster with the security-screening folks at Apple but could later be remotely exploited.
From the report on the project [PDF]:
The key idea behind our attack is that, instead of submitting an app that explicitly contains malicious functionalities to Apple, the attacker plants remotely exploitable vulnerabilities (i.e., backdoor) in a normal app, decomposes the malicious logic into small code gadgets and hides them under the cover of the legitimate functionalities. After the app passes the App Review and lands on the end user device, the attacker can remotely exploit the planted vulnerabilities and assemble the malicious logic at runtime by chaining the code gadgets together.
To test their work, the researchers submitted a proof-of-concept version of their app to the Apple App Store. If installed on a device, it could be used to do sneaky things like posting Tweets to the user’s account, take photos, steal device identity information, send emails and text messages, and attack other apps installed on the device.
“The app successfully passed Apple’s review despite the hidden vulnerabilities and code gadgets that can be assembled to carry out malicious logic,” they write in their paper.
The researchers say they then downloaded the app to a small number of devices on which they then launched remote attacks.
The app was removed from the store immediately after the researchers were able to download it to the devices for testing.
Apple says it has tweaked iOS in response to the researchers’ findings, but is understandably being quiet about exactly what those changes were.
Seemingly benign “Jekyll” app passes Apple review, then becomes “evil” [ArsTechnica]
Remotely Assembled Malware Blows Past Apple’s Screening Process [MIT Technology Review]
Want more consumer news? Visit our parent organization, Consumer Reports, for the latest on scams, recalls, and other consumer issues.

