Well, there’s cheerful news to start off the week: Researchers have discovered and disclosed a massive WiFi vulnerability that puts everyone’s private data at risk. How massive? Basically, if you can read this story, congratulations — you’re almost certainly affected. [More]
hack attack
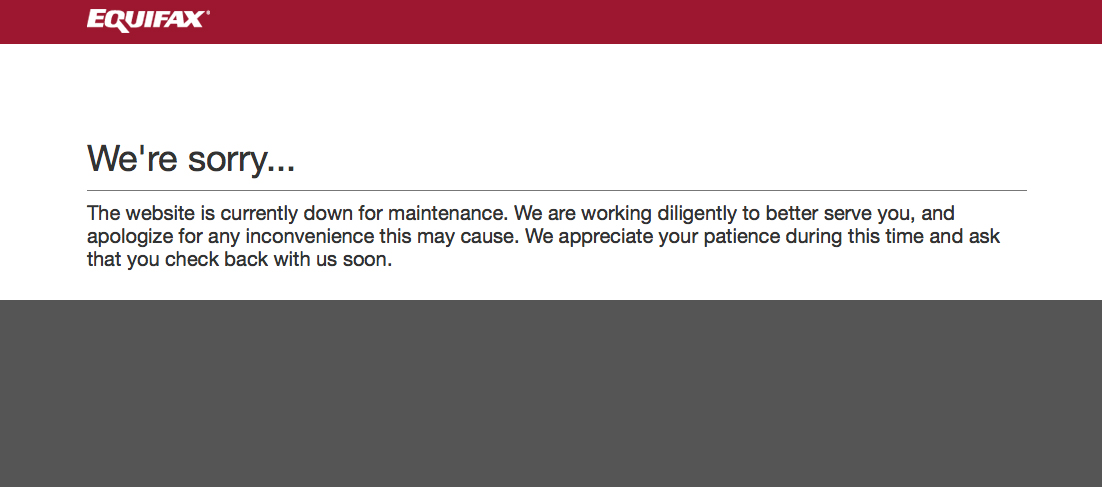
Equifax Takes Part Of Its Website Offline Over Concerns About Malware
Following a report that its consumer-facing website may have been serving up malware to visitors, Equifax — the credit bureau that seems intent on finding every way possible to ruin your day — has pulled some of its web pages offline. [More]
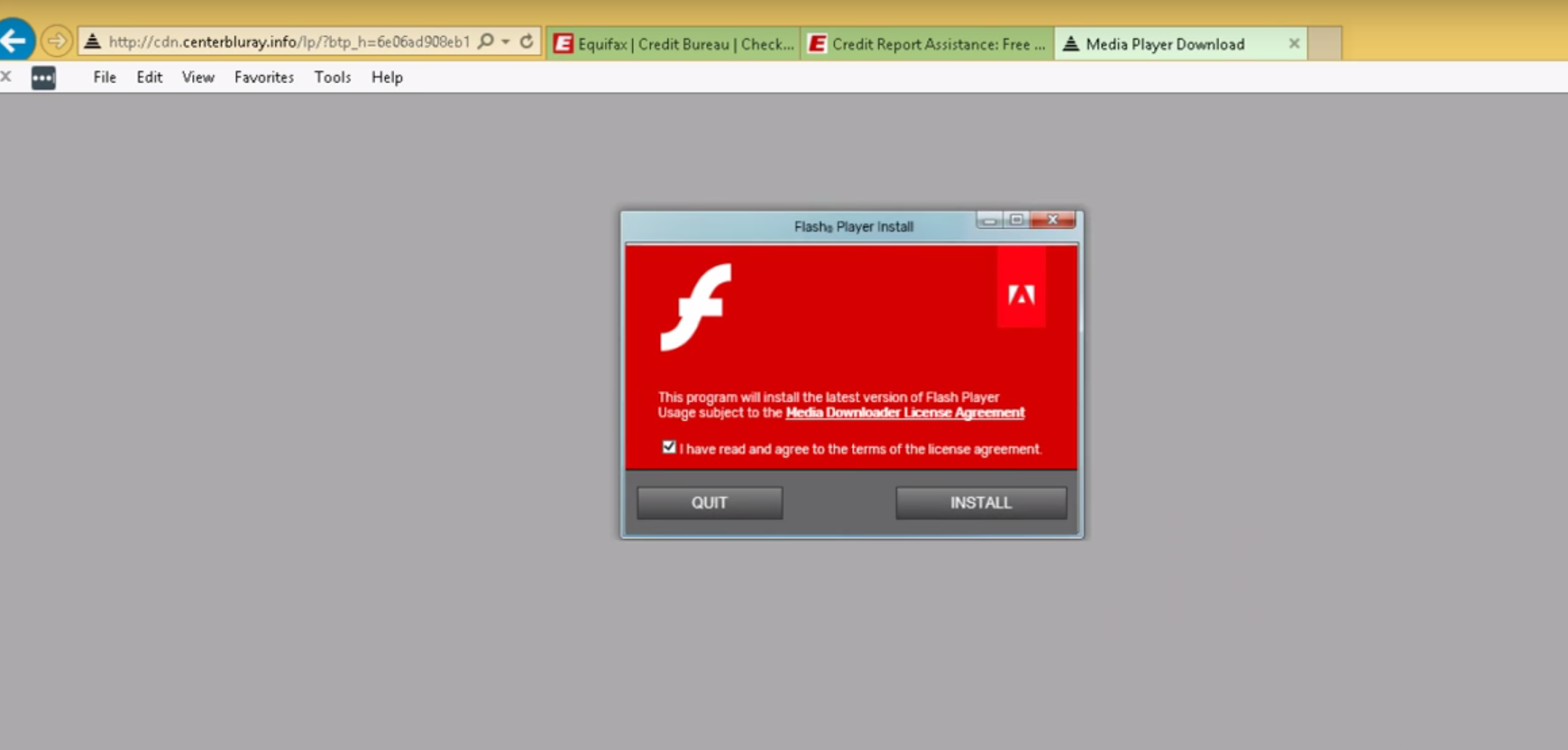
Equifax Website Reportedly Served Up Malware To Some Users
Update: Equifax has taken some pages temporarily offline following the report about malware. [More]

Verizon Now Says That All Yahoo Accounts Were Probably Compromised By Massive Hack
Last year, Yahoo revealed that some 1.5 billion accounts — representing about 1 billion users — had been compromised by a data breach going back years. Now that Yahoo’s new parent company Verizon has had a chance to investigate it turns out that the number of accounts compromised by the hack was… well, every single one of them. [More]

Whole Foods Investigating Credit Card Breach At Some Stores
Have you eaten at or enjoyed an adult beverage at Whole Foods this year? If you paid with a credit card, your information might have been leaked. Whole Foods is investigating a possible credit card breach at some of its stores. [More]

Accounting Giant Deloitte Hit By Data Breach
Following on the heels the massive theft of some 143 million consumers’ information from Equifax, one of the world’s largest accounting firms has confirmed that is the victim of cyber hack. [More]

Two Equifax Execs Exit Company Following Massive Data Breach
The full extent of Equifax’s recently revealed, massive data breach isn’t known yet — although 143 million US customers and tens of millions of others globally are thought to be affected — but top executives are already having to answer for the debacle, with two Equifax officers making a sudden exit. [More]

Equifax Says Site Vulnerability Behind Massive Breach; FTC Confirms Investigation
It’s been a week since credit reporting agency Equifax admitted it had lost sensitive personal data for 143 million American consumers — one of the worst data breaches yet. Now, the company says it knows how the intruders got in… and it’s through a bug that was first identified six months ago. [More]
4 Things To Remember To Avoid Getting Scammed In Wake Of Equifax Breach
As everyone now knows, 143 million Americans had their personal data compromised during a two-month-long data breach at credit reporting agency Equifax earlier this year. Authorities are now reminding consumers to watch out for bad actors looking to profit from everyone’s worries about their newfound vulnerability. [More]

Equifax Announces Data Breach Affecting 143 Million Customers
Credit reporting agencies have access to basically all of our most sensitive financial information, and we pretty much all have our records collected and collated by them whether we want to or not. So that makes it a particularly big problem when one of the big three credit agencies in the country has to announce a data breach affecting all its customers, because that basically means all of us… and this one is bad. [More]

Hundreds Of Android Apps Pulled From Google Play Store After Researchers Discover Botnet
Google pulled nearly 300 malicious apps from the Google Play Store this week, after a team of researchers from several internet companies discovered that they were all hijacking phones’ power into a massive international botnet spanning more than 100 countries. [More]

Stealing Your Identity Can Be As Easy As Stealing Your Phone Number
You’re smart about online security, right? Sure! You use two-factor authentication on all your accounts, you don’t use dodgy WiFi, you make sure to put a passcode on your phone, and you keep it with you at all times, never out of your sight. Unfortunately, that’s not enough to protect you. Because it only takes one thing to hijack your whole digital life: Your ten-digit mobile number. [More]

Hacker Claims To Be Holding HBO Data For Ransom
The saga around a recent hack attack at HBO just keeps getting deeper. Now, hackers that claim to have a whole lot of unreleased programming and potentially embarrassing internal documentation are saying they might not release it… if HBO pays them big bucks to stay quiet. [More]

Someone Remotely Hacked A Segway Scooter
Strapping on a helmet and jumping on the back of a Segway is a popular way for many tourists to take in the sights on vacation. But could your next encounter with such a group involve runaway scooters? It’s possible after a researcher was able to hack into the popular electric scooter and operate it without the help of a rider. [More]

Here’s What You Need To Know About Hard Rock, Loews Hotels Hack Attacks
If you’ve stayed at a Hard Rock Hotel & Casino or Loews Hotel you’ll want to keep an eye on your financial statements after the two lodging companies revealed they’re the latest victims of a hack attack. [More]