Okay, okay, we know what you’re thinking: “Myspace?” you scoff, “It’s 2016! I haven’t had a Myspace account since I was a kid! My gosh, what’s next, CompuServe?” [More]
data theft

Developer Finds Security Hole In SMC Router Provided By Time Warner Cable
If you didn’t provide your own wireless router when you signed up for Internet access from Time Warner, you may have been given an SMC-branded modem/router combo that turns out is ridiculously easy to break into.

American Express Wants You To Use Lame Passwords
We’re no longer indignant about Amex’s weirdly lax security policies anymore, we’re just confused. Why would a major credit card company cold call new customers and insist they give up bank and address info over the phone, or email sensitive data to strangers? Or, we just learned, demand that you use a lame password that isn’t case sensitive, is only 6 to 8 characters long, and can’t contain special characters?

Hackers Discover Data-Stealing ATM At Convention
Nobody knows yet whether it was planted by an attendee, or if the ATM had been there for some period of time before the event, but hackers at last week’s DefCon conference in Las Vegas discovered a rogue unit that was designed to capture customers’ credit card data with each use.

Two Men Charged With Placing Skimmer On Maryland ATM
Two men “of no fixed address” were charged in Maryland earlier this month with tampering with an ATM and skimming funds. The men, currently in custody in Oklahoma for similar crimes, allegedly added a skimmer and camera to an ATM at a Maryland PNC bank in April, but police weren’t notified of the tampering until May 20th.
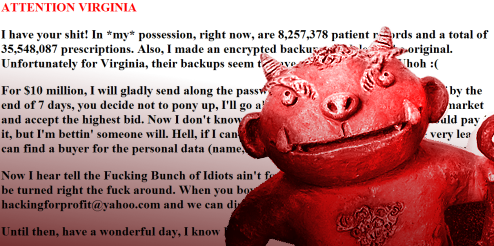
8 Million Patient Records Stolen From Virginia State Database, Held For Ransom
The Washington Post says that a hacker encrypted 8 million patient prescription records from a Virginia state website last week, deleted the backups, and replaced the home page with a ransom note. If the state doesn’t pay $10 million within 7 days, the hacker has threatened to sell the data to the highest bidder.

Visa Covers Butt By 'Delisting' Breached Credit Card Payment Processors
Visa has removed Heartland Payment Systems and RBS WorldPay, the two huge payment processors that suffered recent data breaches, from its list of companies that are in compliance with Payment Card Industry (PCI) rules. It says they can get back on the list when they recertify that they have proper security in place. While this may sound like a significant change in the status of the companies, in reality it does little to change how the three companies do business with each other or with merchants. It’s just a way for Visa to protect itself from any upcoming lawsuits by banks and credit unions against the payment processors.

Another Month, Another Massive Credit Card Data Breach
Don’t be too surprised if you get a letter from your bank or credit union in the next few weeks telling you it’s replacing your credit card. If your data was among the latest set compromised, Visa and Mastercard are already alerting financial institutions so they can cancel the account number.

Three Men Arrested In Heartland Data Breach For Using Fake Visa Gift Cards
The U.S. Secret Service has arrested three men in Florida on “hundreds of counts of credit card fraud” for using fake gift cards imprinted with account info stolen from Heartland Payment Systems last year. The Secret Service still thinks an Eastern European group is behind the Heartland breach, and that the Florida guys are smaller-time crooks who most likely purchased a subset of the stolen data.

DVD Planet Uses 'Ebay' For Password, Sends It To You Via Email If You Ask
Dear DVD Planet, you might want to sit down with the person who designed your customer account system and have a long talk. You know, about things like data security. After we posted this story yesterday about an Amazon shopper who was surprised to find you’d automatically created a barely secure account in his name with his data, another reader—this time a former eBay customer from nearly two years ago—decided to check whether you’d done the same thing to her. Yep! And the password was “Ebay.”

DVD Planet's Automatic Account Creation Raises Security, Privacy Issues
Joel says when he ordered a disc from DVD Planet via Amazon, the company automatically created an account for him on their website. The problem is that the default password they used was so easy to guess that he figured it out on the second try, and he suspects it’s the same password they use on every account. Once you guess it, you can see the customer’s past orders and credit card billing address. When Joel contacted them to have the account removed, he was told that wasn’t possible.

Best Buy Employee Arrested For Stealing Credit Cards
Uh oh, another Best Buy employee has been caught swiping data from customers. Unlike the woman last August who went on small time shopping sprees, this woman was caught using a card reader to swipe and store info on as many as 4,000 customers at the Best Buy store located at 1880 Palm Beach Lakes Blvd in Palm Beach, Florida.

Data On Over 40,000 Patients Stolen From NYC Hospital
The New York Times is reporting this morning that an unnamed employee stole personal data on over 40,000 patients from NewYork-Presbyterian Hospital/Weill Cornell Medical Center. The theft “occurred over the past several years and included patients’ names, phone numbers and Social Security numbers.” As we’ve come to grimly expect in these cases, the hospital was made aware of the theft in January, and announced it publicly on Friday after an internal audit. “We obviously deeply regret that this has happened,” said the hospital’s spokeswoman, Ms. Manners. She also said that investigators are “looking into the possibility that the theft could be part of a larger criminal scheme.”

Red Card! MLSGear.com Shoppers Exposed To Identity Theft
Computerworld is reporting that “a series of SQL injection attacks” on a third-party e-commerce company’s servers has compromised the personal data of customers who shopped at Major League Soccer’s MLSgear.com website. One affected customer told us he received a letter from MLSgear.com letting him know what had happened and offering him free credit monitoring services for a year, which is apparently the standing corporate response to personal data theft.

Consumer Agency IT Pro Admits To Stealing 8.4 Million Records
A senior database administrator for Fidelity National Information Services, a widely used banking technology and data providor, has admitted that he stole 8.4 million customer records from the company and sold the data to a broker, who in turn sold them to marketers. He could face up to 10 years in prison but will probably get less because he confessed. We think he should have to open, read, and shred every piece of junk mail that his victims receive for the next, oh, say 10 years instead.

Lots Of Retailers Don't Use Proper Wireless Security
The recently reported TJ Maxx security breach—where data on 94 million credit card accounts was stolen in 2003, 2004, and 2006—has ended up costing the company $200 million and counting. But although it’s the biggest example so far of retail data theft, TJ Maxx isn’t the only retailer doing a poor job of keeping sensitive data protected from hackers. One wireless security vendor recently surveyed thousands of stores and discovered that a significant number of retailers don’t practice good wireless security:

Hey Consumerists! Get Blacklisted By The Chargeback Bureau!
Welcome to the consumerist blacklist, Dalton Trumbo!