Twitter Admits To Hack, Data For 250,000 Users Accessed

(Bob Reck)
“This week, we detected unusual access patterns that led to us identifying unauthorized access attempts to Twitter user data,” reads a post on the Twitter blog by the company’s Director of Information Security. “We discovered one live attack and were able to shut it down in process moments later.”
An investigation into the attack found that what Twitter is calling “limited user information – usernames, email addresses, session tokens and encrypted/salted versions of passwords” was accessed for those 250,000 accounts.
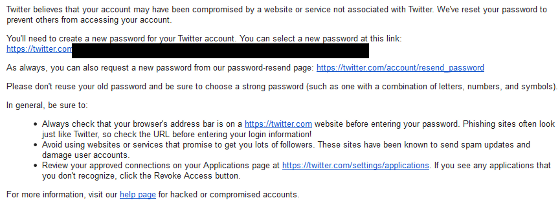
The company says it reset passwords and revoked session tokens for the affected accounts and has is in the process of notifying those that have been affected, who will need to reset their passwords.
“Your old password will not work when you try to log in,” says Twitter.
“This attack was not the work of amateurs, and we do not believe it was an isolated incident,” admits the company. “The attackers were extremely sophisticated, and we believe other companies and organizations have also been recently similarly attacked. For that reason we felt that it was important to publicize this attack while we still gather information, and we are helping government and federal law enforcement in their effort to find and prosecute these attackers to make the Internet safer for all users.”
As the New York Times’ Bits Blog points out, the Twitter post seems to allude to recent concerns about vulnerabilities in Oracle’s Java software. Earlier this month, DHS advised — even after a patch from Oracle — that computer owners disable Java in their browswers “Unless it is absolutely necessary.”
“We also echo the advisory from the U.S. Department of Homeland Security and security experts to encourage users to disable Java on their computers,” writes Twitter, directing users to a Slate article that describes how to disable the plugin.
Below is the copy of the e-mail one reader received about his Twitter account:
Want more consumer news? Visit our parent organization, Consumer Reports, for the latest on scams, recalls, and other consumer issues.