In an attack reminiscent of WannaCry — the ransomware that held servers around the world hostage in May — web servers across Europe have reportedly been hit by another strain of rapidly spreading malware. [More]
viruses

Senator Calls For Investigation Into Office Depot’s Alleged Computer Scanning Scheme
Following a whistleblower report that some Office Depot staffers are allegedly falsely telling customers their computers are infected with viruses in order to sell them on unnecessary repair services, one lawmaker is calling on federal regulators to investigate. [More]

Attack Of The Mutant Emojis: Hackers Used Popular Icons To Breach Messaging Service
Emojis come in all shapes, sizes, and, well, emotions. You might expect the plethora of options to bring a smile to just about any recipient’s face, but you probably didn’t think they would also provide a sneaky access point for hackers. [More]

Company Touts “Ebola Containment Suit” As Literally The Most “Viral” Costume This Halloween
Sometimes I like to think that just once there will be a tragic situation that won’t lead to someone trying to make a buck off a serious situation. But hey, it’s Halloween, when sensitivity to world events apparently goes out the window. So why not charge people $79.99 to dress up in an “Ebola Containment Suit”? [More]

UPS: Hackers Hit Computer Systems At 51 Retail Stores, Possibly Exposing Customer Info
Did I bump my head and wake up in late 2013? Because it sure feels like deja vu with a slew of recent data breaches: Joining P.F. Chang’s, a group of supermarket chains and Community Health Systems in this month’s data breach roll call is United Parcel Service, which says 51 of its retail store locations had their computer systems hacked. [More]

Detect Hardware Trojans With "Singing Rings"
Researchers have proposed a new method for detecting trojan viruses embedded into hardware chips by using voltage detectors that “sing out” in a different frequency when they’re used on a tampered circuit. [More]

Report: Air Force Officials Kept Quiet For 2 Weeks About Drone Virus
When news broke last week that some of the Air Force’s drone aircraft had been infected with a virus, Air Force network security experts reportedly found out about the breach when everyone else did. Officials at a Nevada Air Force base may have known about the problem for as long as two weeks and never reported the issue to security. [More]
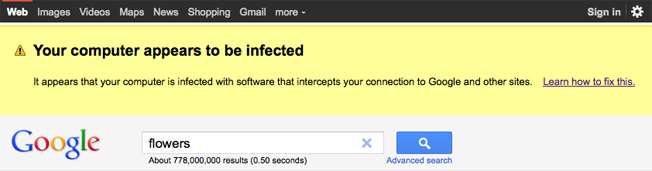
Google Warning Infected Users About Malware
Google has started putting a yellow box with a warning at the top of search results pages for users who may have been infected with a certain kind of malware. [More]

Botnets Rebuild Forces After Rustock Raid
After the Feds and Microsoft in March chopped off the head of the hydra that was the 1-million strong “Rustock” botnet responsible for sending billions of spam, several heads have sprung in its place. PC World notes a Symantec report of a 24% jump in emails containing malicious links and attachments, possibly representing an attempt to regrow the forces of zombie controlled computers and fill the void left by Rustock. [More]

Badware Hosting Sites Growing More Sophisticated, Offer Menu Of Services
The illicit economy of phishers and malware perpetrators is growing more sophisticated, and more brazen. “Bulletproof” hosting sites that offered to protect their users from attacks and takedown requests now have corporate-like web pages offering a menu of a la carte services. The only limit is no spam and no porn. Hey, even they have standards. [More]

Search Online For Cameron Diaz At Your Own Risk
I have no idea why anyone would be searching online for Cameron Diaz screensavers, but according to McAfee, if you feel the need to fill up your monitor with a pic of the thespian, you’re putting your computer in harm’s way. [More]
Should You Abandon McAfee Or Take Their Free 2-Year Extension?
If you use McAfee’s anti-virus program and have Windows XP with SP 3, you may have noticed last week that your PC was shutting down every 60 seconds. That was because McAfee pushed out an update that it now admits wasn’t properly tested. To apologize, the company says it will reimburse you for repairs (although it hasn’t provided details on this yet), and it’s offering everyone who was affected a free 2-year extension of the service. Should you take the offer and call it even? Seth Rosenblatt at Cnet says you shouldn’t bother. [More]

Don't Let Your Battery Charger Expose Your PC To Hackers
If you’re using the Energizer Duo battery charger, and have connected it to your PC to check the charge levels of the batteries, you may have inadvertently exposed yourself to a program that could give hackers access to your computer. The charger has been discontinued, and Energizer recommends removing the software along with the file that enables the backdoor. [More]

Don't Let An Unknown Caller Talk You Into Downloading Software
In the wide world of scams, this combination of a phone call and computer malware is sort of a novel twist. Jay likes to string phone scammers along to waste their time, so he managed to get quite a few details about how this particular scam works. If you’ve got naive family members with access to computers, either take away their computers or tell them never to download software from a stranger on the phone. [More]
Why Is Spam Around? Because 12% Of Readers Actually Try To Buy The Stuff
Why, in a rational world, does spam continue to exist? Because someone you know—or maybe it’s you—has actually tried to buy something from it, a new study finds. Find that person and beat him (or yourself) with a stapler.