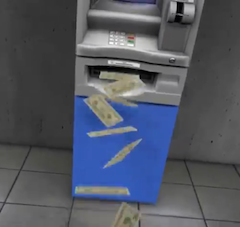
New Malware Activated By Text Message Makes ATMs Start Spitting Cash
(Symantec)
This text-and-spew scheme works on a certain type of standalone ATM, according to security vendor Symantec in a blog post yesterday (via PCWorld). The software is called “Ploutus” and was first spotted in Mexico.
Symantec isn’t saying which kind of ATM can be hit with this malware, but did test the system out on one of the machines to see how it works.
Installing Ploutus is tricky, and villains would have to access to the machine in order to jerry-rig it to barf cash. That’s likely why standalones are more at risk, as they’re more exposed than the kind nestled into a bank of ATMs.
The whole set-up is controlled from a distance by a text message, with an infected phone connected inside the also infected ATM to a USB port.
“When the phone detects a new message under the required format, the mobile device will convert the message into a network packet and will forward it to the ATM through the USB cable,” writes Daniel Regalado, a Symantec malware analyst.
From there, a “money mule” or someone else hired to be the cash collector grabs the dough and carts it off. And there’s no skimming off the top, either — whoever is in charge knows exactly how much money the ATM will spit out.
Symantec is warning that because most ATMs are still running outdated Windows XP, companies need to get serious about protecting their cash, as “the banking industry is facing a serious risk of cyberattacks aimed at their ATM fleet.”
Check out Symantec’s handy video below for more info on how the whole thing works:
Texting ATMs for Cash Shows Cybercriminals’ Increasing Sophistication [Symantec]
Text message command makes infected ATMs spew cash [PCWorld]
Want more consumer news? Visit our parent organization, Consumer Reports, for the latest on scams, recalls, and other consumer issues.

