You generally expect that a company that has your personal information — like your address, recent orders, and billing information — is going to treat that data with some level of care. While you know their privacy policy might still allow some sharing for marketing reasons, you don’t expect their customer service agents to divulge it to anyone who happens to call up and pretend to be you. [More]
social engineering

How Social Engineering Fooled Amazon Customer Service Reps Into Sharing A Customer’s Data

Fake Boss Wire Transfer Scammers Have Now Stolen $1.2 Billion From Companies
All year, we’ve been sharing information about a scam hitting companies all over the world, where very clever and resourceful scammers impersonate bosses and extract money on false pretenses. The best protection against this kind of fraud is education, and while law enforcement are doing their best to let people know about the scam, the number of victims is only increasing, and law enforcement estimates that the scammers have drained $1.2 billion worldwide from businesses’ bank accounts. [More]

Would A Shopping Cart Mirror Showing Your Fat Face Make You Buy More Vegetables?
Could you look yourself in the eye, then load your grocery cart up with root beer and ice cream bars? No, literally. Stakeholders ranging from from physicians to grocers want Americans to buy (and eat) more fresh produce and less junk food, but how can they do that without a complete overhaul of the food system? With gentle nudges. [More]
Try These Search Terms If You Want Some Malware
Computer virus company McAfee has assembled a list of the top search keywords that are most commonly linked to malware exposure. The winning phrases are: word unscrambler, lyrics, myspace, free music downloads, phelps, game cheats, printable fill-in puzzles, free ringtones and solitaire. In addition, the general categories that are considered riskiest are: screen savers, free games, work from home, Olympics, videos, celebrities, music and news.
../..//2009/04/09/it-turns-out-that-weird/
It turns out that weird evening bank verification call from AmEx was legit. Brandon wrote back, “After reading all the comments on Consumerist, it stoked my fear of fraud even more, so I called Amex security. They verified the call was legitimate and was from American Express. It was just poor customer service after all.”

Amex Wants To Play "Scam Call" With You, Please Participate
Update: It turns out the call was legit.

Reminder: Text Messaging Can Be Used For Scams, Too
This story from Jessica is a good reminder that scammers don’t care about the technology, they care about about fooling you. That means they’ll use whatever method is available—in this case, SMS.
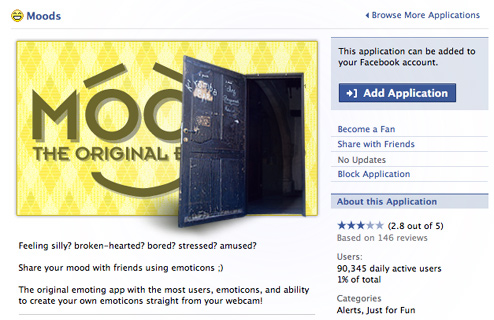
Are You Sure You Want To Add That Facebook App?
Gregory writes in to point out that Facebook does a lousy job of monitoring the development of its third-party Platform applications—and in fact many of them are written so badly that they can be easily hacked. The examples he cites, which are listed in the winter issue of the hacker magazine 2600, are all fairly mild stunts like spoofing user IDs, changing the moods of another user, and re-routing gifts, “but this information could be used to mount large scale social engineering attacks if automated and coupled with other information.” To illustrate how easy it is to change another user’s settings, he pointed us to a YouTube example of how to change another users “mood” via the Mood app.
Hacking US Airways' Company Directory To Reach Lost And Found
Here’s the recording of us, spruced up by the visual wizardy of our video slave Alex Goldberg, calling Investor Relations (480-693-1227) yesterday, pressing 0, and brute forcing our way to somebody, anybody, any live person to help us just file a simple (and yes, probably totally hopeless) Lost and Found request.
AUDIO: Comcast Easily Tricked Into Giving Your Personal Info To Wiseass Teenagers
Like many companies, Comcast doesn’t train its customer service reps enough in security verification. The result is that anyone can call up, pretend to be a service tech, and get your info. Criminals can pick up pieces from one company and use them to get more information out of another, and so on. They can use the end result to steal your identity, your bank account information, and other fell deeds.


