We told you the other day how several electronics manufacturers were shipping products with default username and password combinations that many people never think to change, leaving them open to being compromised by hackers and pranksters. To help those consumers who may not want to get into the gritty details of that story, here’s a quick guide to a number of popular types of products that people may not know they need to change the password to. [More]
passwords

If You Didn’t Change The Default Password On Your Security Camera, Someone’s Probably Watching It Stream
Remote access has been a boon to many industries. Home security cameras, for example: not only can you keep an eye on your property in case anything bad happens, but you can do it in real-time, instead of reviewing footage after the fact. But cameras protecting the security of your home may in fact need a serious security helper of your own. And running tens of thousands of searchable livestreams from unwitting camera owners who didn’t change default the access passwords on their devices is certainly one (unethical, intrusive) way to make the point. [More]

eBay Says Etsy Is Wrongity Wrong To Blame It For Spam Problems
Yesterday, we reported that the craft honchos who run Etsy have noticed an increase in hijacked accounts sending out spammy messages, and they put at least some of the blame on users with the same passwords on both their Etsy and eBay accounts. However, eBay counters that this is not their fault, since unencrypted passwords weren’t part of last month’s account data breach. [More]
Spammers Take Advantage Of eBay Breach, Invade Etsy
When the usernames and passwords of a big, popular site like eBay are compromised, consequences can spread beyond the original site that was attacked. It’s possible that users of selling platforms Etsy and eBay use the same usernames and passwords on both sites, since security staff at Etsy say that they’ve noticed an uptick in spam and account hijackings since the recent eBay breach. [More]
87-Year-Old Inventor Of Computer Password Keeps His On Sheets Of Paper
Do you have so many online accounts that you can barely keep track of where you’re registered, let alone what the passwords are? You’re certainly not alone. Heck, even Fernando Corbató, a retired researcher who is one of the people credited with inventing the computer password 50 years ago, keeps all of his on a few typed sheets of paper. [More]

‘Password’ No Longer The King Of Bad-Idea Passwords
No matter how frequently consumers are warned about creating predictable passwords, many just aren’t getting the message. The good news from the latest survey of leaked passwords is that the most frequently used password is no longer “password.” The bad news is that the new bad-password champ is equally idiotic. [More]

Security Questions Aren’t Very Secure When Your Whole Family Knows The Answers
If you’re a forgetful person or have too many accounts to keep track of, the ability to reset an account password by typing the answers to a few questions about yourself can be a lifesaver. But there’s a dark side, too: it leaves you vulnerable to social engineering. Or having your Amazon password reset by your 94-year-old dad. [More]
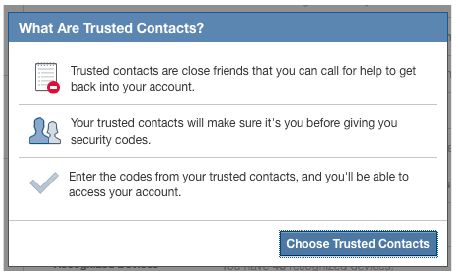
Facebook Lets You Assign ‘Trusted Contacts’ To Help You Access Your Account After Being Locked Out
Lots of people give an extra set of house keys to close friends or family in case they get locked out. So why not have a similar way of dealing with those times when you’re locked out of your Facebook account? [More]

Someday Your Brain Could Replace All Those Pesky Passwords With “Passthoughts”
There’s perhaps nothing more unique than your brain. And because we don’t yet live in a world where villains can hack into your thoughts (key word: yet), the next innovation in passwords could do away with those typed phrases and combinations of letters, numbers and punctuation and replace them with your thoughts. [More]

Apple Solves iTunes Account Problem By Locking You Out Of Account
Michael was having a pretty minor problem with playing television programs in iTunes. Sure, it doesn’t even rank as the a serious first world problem, but he contacted Apple to get it resolved, because that’s what Apple is supposed to do. A senior representative tried to resolve the problem by resetting his iTunes password. Nice idea if it had worked. It didn’t. Now this cord-cutter, who uses his Apple TV to catch up with favorite shows, can’t watch those shows at all. Being locked out of his iTunes account and all. [More]

Heads Up: Using The Word "Password" In Your Password Is A Terrible Idea
File this one under “D” for “duh” — the easiest way for someone to break into protected accounts is by guessing your password because many of you just use that same word as part of said password. C’mon, people, get a little creative. [More]

How To Create A Strong Password And Remember It
Following the hack of Zappos.com and 6pm.com there are probably quite a few of you looking for a way to create strong passwords and also remember them. Back in December, our safety-conscious friends at Consumer Reports ran a guide to creating strong passwords that are also easy… well, easier, to remember. Here it is. [More]
Video Of 25,727 Passwords From The Sony Hack, One Per Frame
Stare agog as all the the passwords released in the Sony LulzSec breach race past your eyes in this video. [More]

Website Offers Peace Of Mind About Security Of Your Email Password
Back in my day, I had to walk five miles in the snow to make sure my password was safe, but now, what with all the hacking going on, there are easier ways to check if yours has already been compromised. Like a handy dandy website, for one. [More]

If You Use One Of The Most Common iPhone Passcodes, Stop It
One way to make things easy for identity thieves is to choose an unimaginative, easy-to-remember PIN that tons of other people are using. [More]

Hackers Swipe Emails, Addresses And Passwords From Video Game Site
These are not the best of times to be a gamer who leaves personal information on websites. In addition to the Sony troubles of the past couple months, British game publisher Codemasters has been hacked, leaving emails, addresses and passwords exposed. [More]

Tennessee Lawmakers Pass Bill Making It A Crime To Share Your Netflix Password
If you’ve ever let a friend or family member know your password for subscription services like Netflix or Rhapsody so they can watch a movie or listen to a song, we hope you don’t live in Tennessee, where state legislators have passed a bill making it a crime. [More]