In the wake of two data breaches at hotels operating under the Trump Hotel Collection umbrella, the attorney general for the state of New York has reached a settlement with the company that involves a small financial penalty and promises of improved data security. [More]
malware

Credit Card Numbers Aren’t Worth Much Now, So Hackers Want Your Mobile Banking Info
If you’re worried about the security of mobile banking, you’re not alone. Mobile banking apps use a wide array of complicated passwords, biometric tools (like thumbprint or facial scanning), and two-factor authentication to make sure you’re you before “you” try to mess with your money. But preventing anyone from being able to guess how to log in to your account does no good if your phone’s got malware on it that gives would-be baddies a wide-open back door. [More]

Data Breach At 20 Hotels In 10 States May Have Exposed Guests’ Payment Card Data
The operator of several hotels across 10 states and Washington, D.C. — including Starwood, Marriott, Hyatt and Intercontinental locations — says guests may have had their payment data exposed by hackers who targeted the businesses with malware starting last year. [More]

Big Bunch Of Legitimate Business Websites Hijacked To Deliver You Bad Malware
You know to avoid sketchy sites, and always double-check your URLs. You like to think that going to a legitimate business website is going to be pretty safe, malware-wise. But alas, even the most legitimate site is vulnerable to security flaws… and a whole wave of them have recently been hijacked to try to extort money from you. [More]

How To Avoid Shady Third-Party Apps Piggybacking On Popularity Of Pokémon Go
Amid the crowds of roving Pokémon Go players out there following virtual monsters around with their phones, there are likely some who might be interested in downloading third-party or ancillary apps to help you in your quest. But like with any popular tech phenomenon, there could be dark forces lurking out there, shady apps that you should avoid. [More]
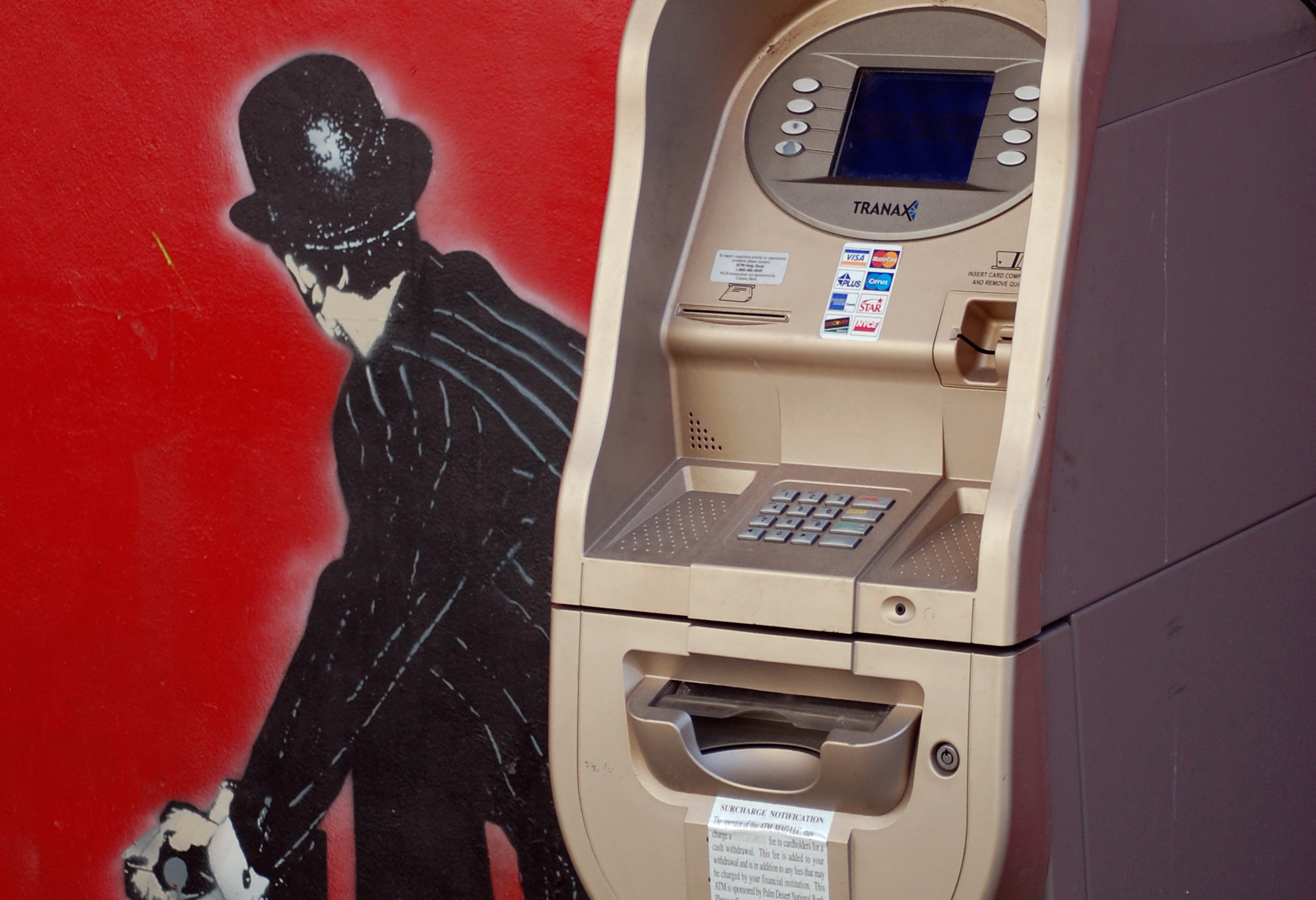
New And Improved Version Of Popular ATM Malware Spotted In The Wild
Modern ATMs are just computers attached to machines stuffed with cash, and that means that ATMs can also be infected with malware and viruses. Back in 2009, a piece of malware that could make an ATM spit out cash or give out the card numbers of people who had recently used the machine was found in the wild, the not-very-creatively-named Skimer. Now the security company Kapersky Labs has discovered a new and better (if you’re not a bank or a consumer) version of Skimer out in the wild. [More]

Investigation At Wendy’s Turns Up Malware, Payment Breach At 300 Restaurants
Remember the suspected payment data breach at Wendy’s restaurants from earlier this year, which resulted in a class action lawsuit almost right away? It took a few months, but Wendy’s has confirmed that they did experience a breach dating back to fall 2015, and they’ve now fixed the underlying problem, which affected an estimated 5% of their restaurants. [More]

Trump Hotel Collection Investigating Another Possible Customer Data Breach
Last fall, we learned that payment systems in Trump Hotel Collection properties had been compromised with malware, compromising customers’ payment card numbers for more than a year. Now reports from the banking industry indicate that there might be another breach in one or more Trump hotels –– the second in less than a year. [More]
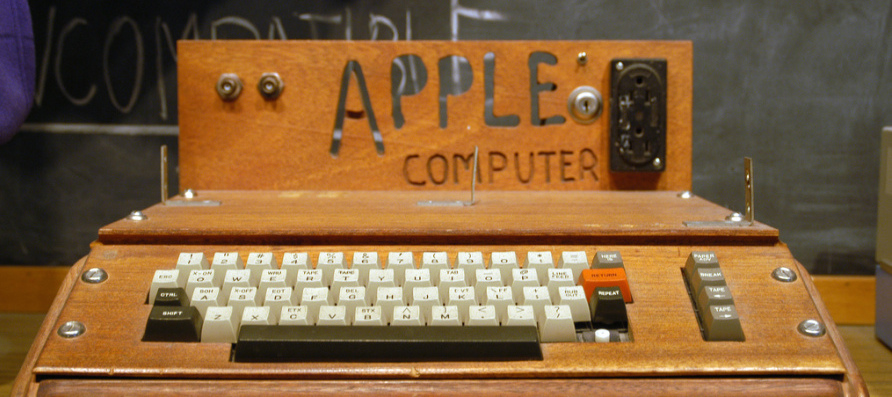
Apple Users Targeted With Widescale Ransomware Campaign For First Time
For decades, many Apple users have bragged about their computers not being targeted by viruses and malware in the way that Windows-based computers were. But over the weekend, hackers launched what is believed to be the first widespread ransomware campaign against Mac computers. [More]
IRS: Email, Text Scams Targeting Taxpayers Up 400% This Year
It’s tax season, which means it’s the prime time for scammers to crawl out from underneath their scammy rocks and try to nab taxpayers’ personal info. So far, this year’s electronic tax scams are even more prevalent than before, the Internal Revenue Service says, surging 400%. [More]

Protect Your Heart (And Wallet) From These Valentine’s Day Scams
This is the year. It’s the year you’ll wake up on Feb. 15 without the stinging sensation of intense regret that inevitably follows after mourning Valentine’s Day at the bottom of a booze bottle, covered in bits of melted chocolate stuck to you in your sleep, because your beloved turned out to be a scammer. Because this year, you’re going to be prepared for any romance scams that may come your way. [More]

Hyatt Confirms 250 Hotels Were Infected With Malware Last Year, Possibly Exposing Customer Payment Data
After announcing late last year that a slew of its hotels had been infected by malware, Hyatt has now identified the 250 properties that were affected — roughly 40% of its businesses in operation. Customers staying at those hotels who paid with a debit or credit card may have had their payment data and other information exposed to hackers, the chain said. [More]

Starwood Hotels Reports Payment Systems At 54 Locations Infected With Malware
Just days after Starwood Hotels and Resorts made headlines for combining with Marriott to make the world’s largest hotelier, the company is back in the news for a decidedly less exciting issue: it’s the latest victim of a hack attack. [More]

Apple, Google Pull Unofficial Instagram App That Harvests Usernames And Passwords
In yet another example of why unofficial apps aren’t always to be trusted, Apple and Google have yanked an app from their app stores that was supposed to let users know who was viewing their profiles. That’s not a thing, and a developer says that the app instead acted as malware, secretly collecting usernames and passwords and using them to post spam to users’ accounts. [More]

Apple Pulls Malware-Infected Apps After App Store Suffers Its First Major Breach
Hackers have finally taken a bite out of Apple’s App Store: the company confirmed that attackers were able to infect some of the apps it offers with malware, by copying and modifying a tool used by software developers. Apple says it has now removed the affected apps from the App Store. [More]

Hackers Swipe 225,000 Jailbroken iPhone Users’ Account Information
Jailbreaking your Apple device, or using illicitly obtained software to customize it in ways that Apple never intended and install unauthorized apps, is something that most users thought was against the rules but innocent, even if it does void your Apple warranty. Now Apple is facing a good news/bad news situation: a hack involving jailbroken iPhones validates their policies, but also means that the phrase “iPhone hack” is all over the news. [More]



