Another thing that can suck about having your identity stolen is that the crook can rack up crimes in your name. That’s what happened to one University of Georgia student who opened up the campus paper to find his name underneath the mug shot of another young man for a DUI, reports Red And Black. [More]
identity theft

Mike Fights The Identity Thieves
Someone stole Mike’s identity and has been using it to pay for gas service and buy cellphones in his name. He’s even got a $163 default judgment against him for something he never paid. Here’s how he unraveled the threads of his identity thieves, and how he may never truly be free from their grasp. [More]

Fire Up That Shredder To Protect Yourself From Identity Theft
We’re hoping that by this time in the wide world of the Web that most consumers are taking steps to protect themselves from identity theft online, but hey, wait a minute! What about the good old-fashioned paper theft? [More]

Bank Of America Sides With Fraudster, Holds Money Hostage
Some criminal has joined with Bank of America to make John’s life hell. Multiple fraud investigations have froze what little of John’s money remains after overdraft fees have sucked it dry before BofA decided there were no errors or fraud on his account. Fed up, John has closed his account but wants his money back. [More]

Your Facebook Login Can Get Jacked By A Monkey With A Mouse
The guy sitting next to you in the coffee shop might actually be logging into your Facebook account, using the info beaming out your computer. It’s called “session hijacking” or “sidejacking” and despite it being a well-known vulnerability, most websites aren’t protecting their users from it. After a developer recently unveiled a user-friendly bit of code that makes “sidejacking” as easy a few mouse clicks, the problem is getting fresh attention. [More]

ID Theft Victim Receives Ceaseless Cavalcade Of Stolen Packages
This lady’s address was used by credit card thieves who were scoping out different merchants’ fraud triggering levels. Which meant that she was receiving packages for and calls about a portable night light, Vietnamese movies, and a $2,500 Gibson. Every day for two months she got something new, and no one could stop it. [More]

PayPal Thinks I Stole My Own Identity, Won't Give Me My Dollar Back
April is thankful she didn’t keep a bunch of money in her PayPal account because she can’t touch the buck and change she has left in there. Her crime: moving and failing to convince PayPal she’s the same person. She says PayPal won’t let her re-activate or close the account no matter how much proof she provides. [More]

Bank Closes Hacked Account Without Telling Me, Goes For Upsell
Virginia discovered her Netflix DVDs stopped flowing because Wells Fargo disabled her credit card, apparently without notifying her. When she called to see what was up, she got an opportunistic upsell. The bank rep told her the account was closed because it had been “compromised” then offered her a $12-a-month protection plan to quell future compromising. [More]
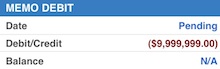
Chase Freezes Long-Time Customer's Accounts With $9.9 Million Overdraft Fee
Chase froze Micah’s checking accounts with a $9.9 million overdraft fee after he took the ultra-suspicious step of opening a joint checking account with his girlfriend. Rather than merely freeze the joint checking account, Chase decided to freeze all of Micah’s assets until they could verify that their customer of thirteen years was really whom he said he was. Not even a letter from the Social Security Administration, handed to the local Chase branch and sent to Chase’s fraud unit could stop Micah’s debit card from being canceled. Now Micah has no access to his cash, a $9.9 million charge to his name, and still no joint checking account with his girlfriend. [More]

iTunes Hackers Raid Accounts, Charge Untold Amounts
While iTunes users were barbecuing and preparing for fireworks this weekend, hackers smoked their accounts, buying apps with stolen money to drive specific apps up the sales charts. [More]

Authorities Bust International Credit Card Cloning Ring
Over 170 people around the globe were arrested on suspicion of participating in a massive credit card scam, reports Reuters. Fourteen countries were involved, and although most of the arrests were in Spain, there were also raids and/or arrests in Romania, France, Italy, Germany, Ireland, Australia, Sweden, Greece, Finland, Hungary, and the United States. In all, police say they discovered at least 120,000 stolen credit card numbers. [More]

"Got ID?" Is A Question Many More Businesses Will Be Asking Soon
Your driver’s license could start getting worn down a lot starting in December . That’s because a whole bunch of businesses will soon be required to ask you for your ID, everyone from your dentist to your car dealer. [More]

86-Year-Old Receives Surprise $19k Bill From Macy's
Lorene Pounds is 86 years old and says she hasn’t shopped at Macy’s in years. That’s partly why she was surprised when Macy’s called her up and told her she was delinquent on her credit card account. The other reason she was surprised was they said she owed $19,791. [More]
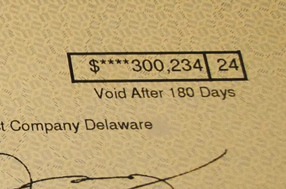
Fidelity Sent Me Someone Else's $300,000 Retirement Savings
Douglas received an unexpected delivery from UPS last week: a check from Fidelity Investments made out to Vanguard Fiduciary Trust Company for over $300,000, along with a bunch of 401(k) rollover paperwork that included the real account holder’s address, date of birth, SSN, and phone number. [More]
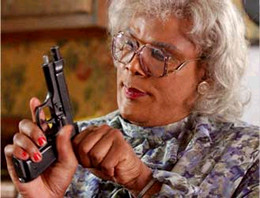
Okay, Who's Been Using Tyler Perry's Credit Card?
Writer/director/actor Tyler Perry updated his website on Friday with a friendly letter to his fans. He talked about wrapping up his latest theatrical tour, and how beautiful his vacation spot was, and then ended on a strange note: “By the way, some idiot stole my credit card number. Can you believe that? Take a look at all the stuff they charged. If you know any of these people, call the police.” The charges, mostly airfares between L.A., Las Vegas, New York and Fort Lauderdale, came up to more than $28,000. [More]

Why Phishing Works Even If You're Not Normally Stupid
If you spend a lot of time online, you’re probably aware of phishing scams and know what to look out for. In other words, you’re not one of those ignorant types who clicks on links and starts entering personal information without hesitation. Writer and blogger Cory Doctorow is what you might call hyper-vigilant–he keeps unique passwords, uses a VPN when going online in public, and generally knows not to trust strangers. Still, he got phished a couple of weeks ago. [More]