A certain Scarlett Johansson photo you may have read about but certainly didn’t check out yourself is part of a federal investigation that resulted in the arrest of a 35-year-old Florida man who is accused of hacking into online accounts of various celebrities. [More]
hacking

Man Who Hacks Neighbor's WiFi And Tries To Frame Him For Crimes Gets 18 Years
Good firewalls make good neighbors, but they won’t stop a determined hacker from busting through and manipulating your cyber footprints. For proof, look at the Minnesota man convicted of hacking his neighbor’s WiFi and attempting to frame him for child pornography and other crimes will serve 18 years in prison. [More]

Website Offers Peace Of Mind About Security Of Your Email Password
Back in my day, I had to walk five miles in the snow to make sure my password was safe, but now, what with all the hacking going on, there are easier ways to check if yours has already been compromised. Like a handy dandy website, for one. [More]

Erotic Phishing Attack Steals Thousands Of Tumblr Logins
Thousands of logins for emo-blogging platform Tumblr have been stolen in the past week via a phishing attack that lured users to enter their credentials in exchange for the promise of erotic content. [More]

Hackers Breach Nintendo 3DS Defenses Right After Device Debuts In Japan
A major reason for a video game company to come out with a new device is to make it safer from attacks by modders who find ways to let the systems play unlicensed games, as well as swipe copies of legit titles. Nintendo’s honeymoon for the 3DS handheld — which was just released in Japan and comes to the U.S. in late March — is now over before it really started. [More]

Credit Card Hacker And ID Theft Forum Overlord Sentenced To 13 Years Prison
Max Vision, the security consultant who was first sent to prison in 2001 for messing with the Pentagon, has now been sent to 13 years in prison for “stealing nearly two million credit card numbers from banks, businesses and other hackers,” reports Wired. The FBI took a renewed interest in Vision in 2006 after he successfully made a power grab on several competing black market ID theft websites. “I’ve changed,” Vision wrote in a letter to the court, and although he faced life in prison, he was given the shorter sentence partly because he’d cooperated with the government. With good behavior he’ll be back out in 2018. [More]

28-Year-Old Pleads Guilty To Stealing Over 130 Million Credit And Debit Card Numbers
Albert Gonzelez pleaded guilty today to “conspiracy to engage in wire fraud for his role in stealing more than 130 million credit and debit card numbers from Heartland Payment Systems,” reports Boston.com. [More]
State Job Website Has Great Opportunities For Self-Starting Identity Thieves
CBS 5 exposed a “gaping hole” in the code of California’s state-run employment website that allows anyone who views the site to access and modify other users’ resumes and personal info simply by changing some numbers in the URL.

Founder Of FlyersRights Says Delta Hacked Her Email Account
Kate Hanni, the founder of the passenger advocacy group FlyersRights.org, has filed a lawsuit against Delta Airlines in which she claims they hacked her email account and acquired personal email messages sent between her, some journalists, and a guy who was at the time working for Metron, a company hired by the FAA to investigate Delta.

Ameriprise Bans "Customer Advisor" For Posting Link To Consumerist
Hey, we helped get an Ameriprise customer banned from the financial company’s consumer advisory panel! Sorry about that, Brendan.

Another Sears.com Security Hole Discovered
That Sears website exploit we posted about a couple of weeks ago was funny, mainly because it seemed more embarrassing for Sears than a true security risk. However, an independent security researcher had also discovered a more significant issue with the site—it allowed for an unlimited number of gift card verification attempts via an external script, so a criminal could use the site as a brute force method to identify valid gift cards for Sears and Kmart.

Ameriprise Website Riddled With Security Vulnerabilities For At Least Five Months
[Note: The original headline for this post mistakenly identified Ameritrade as the subject of the post. It is actually Ameriprise Financial. I deeply regret the error.] Since March of this year, security expert Russ McRee of HolisticInfoSec.org has sent 6 messages to Ameriprise Financial warning them of easily exploitable security holes on their website. They ignored every request, while at the same time reassuring customers that “No one without the proper web browser configuration can view or modify information contained on our systems.”
Apple Blames Jailbreaking For Recent AT&T Visual Voicemail Outages
Apple’s not through with their blitz against jailbreaking, with this newly updated support doc that says, among other things, that the recent Visual Voicemail outages from AT&T were caused by—and happened to—hacked iPhones.

Hackers Smack Down Latest iPhone Firmware, Unlock New Phones
For as long as there have been iPhones, there’s been the requirement to sign up for AT&T service. And as long as that requirement has been around, there have been hackers who release downloads that unlock your phones and free them to access other services.
Apple Wants To Make Jailbreaking Worthy Of Jail Time, $2500 Fine
[it] would have the right to claim statutory damages of up to $2,500 “per act of circumvention.” People who jailbreak phones, might even be subject to criminal penalties of as long as five years, if they circumvented copyright for a financial gain.

Did Turkish Police Beat Information Out Of A Suspect In The TJ Maxx Credit Card Case?
Christopher Soghoian over at Cnet is reporting that Turkish police may have used violence to get the encryption keys of one of primary ringleaders in the TJ Maxx credit card theft investigation. The suspect, Maksym Yastremskiy, is apparently a “major figure in the international sale of stolen credit card information.”
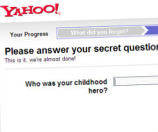
Online 'Security Questions' Can Be Too Easy To Crack
The ease with which a student was able to reset Sarah Palin’s Yahoo email password highlights a vulnerability of so-called “challenge questions” designed to verify your identity: if the questions are about personal details from your life, there’s a risk that somewhere out there on the web, that info is visible to the public. That might be a realistic risk only for public figures, but it’s also possible that friends or family members could answer your questions with a little guesswork. If you want better security, make up fake answers that you’ll remember.



