Adobe Flash is doing a great job this week of keeping up its track record as one of the buggiest, least secure, most vulnerable pieces of software ever to hit the web. On the heels of a recent update, researchers have found a massive exploit in Flash that affects every single version of the software, on every single platform. So yes, if your computer has Flash, that means you, too. [More]
exploits

Android Bug Can Let Basically Anyone Bypass Your Lock Screen If You Use A Password
It is just not a great year for Android security, it seems. Researchers in Texas have discovered that some devices running Android version 5 (Lollipop) can be unlocked and accessed basically by just mucking around with buttons on the lock screen long enough. [More]

Bad News: Security Hole Can Let An Attacker Take Over Your Android Phone With A Single Text
It’s a bad news Monday for up to 950 million — yes, that’s almost 1 billion — Android device owners worldwide. A vulnerability that would let a hacker take over your phone remotely has been announced, and it’s a doozy. [More]

New Exploit Leaves Up To 600M Samsung Galaxy Phones Vulnerable To Hack
Bad news for up to 600 million Samsung Galaxy phone owners worldwide: a big fat new vulnerability has been found that could let anyone with the inclination to cause trouble into your phone to read your messages, listen to your mic, watch your camera, and push malware at you. Oops. [More]

Don't Press The F1 Key
Windows: pressing the F1 key might make your computer go boom. A security exploit deployed by certain malicious websites hides in the Windows help files and could get launched if you press the F1 button. It will only happen, if the following is true: [More]

Ameriprise Bans "Customer Advisor" For Posting Link To Consumerist
Hey, we helped get an Ameriprise customer banned from the financial company’s consumer advisory panel! Sorry about that, Brendan.

Another Sears.com Security Hole Discovered
That Sears website exploit we posted about a couple of weeks ago was funny, mainly because it seemed more embarrassing for Sears than a true security risk. However, an independent security researcher had also discovered a more significant issue with the site—it allowed for an unlimited number of gift card verification attempts via an external script, so a criminal could use the site as a brute force method to identify valid gift cards for Sears and Kmart.

Ameriprise Website Riddled With Security Vulnerabilities For At Least Five Months
[Note: The original headline for this post mistakenly identified Ameritrade as the subject of the post. It is actually Ameriprise Financial. I deeply regret the error.] Since March of this year, security expert Russ McRee of HolisticInfoSec.org has sent 6 messages to Ameriprise Financial warning them of easily exploitable security holes on their website. They ignored every request, while at the same time reassuring customers that “No one without the proper web browser configuration can view or modify information contained on our systems.”
Flawed Sprint Security Worse Than We Thought
In the comments on our post exposing a flaw in Sprint’s online account security that would let a stranger completely take control of your cellphone account, a former Sprint rep says it’s even weaker than what we thought. How? Reader Dragonfire81 says that every question about cars has three luxury models and one typical car, making it pretty easy to guess. “None of the above” for “which properties have you owned” was correct 99% of the time. And worst of all, you only need to answer two of the questions correctly to gain access to an account. “I was shocked at the number of times I was able to access an account by simply guessing the answers,” he writes. “Fortunately I am an ethical person, but if I wasn’t I could’ve done a LOT of damage very easily.” Here’s his comment in full:
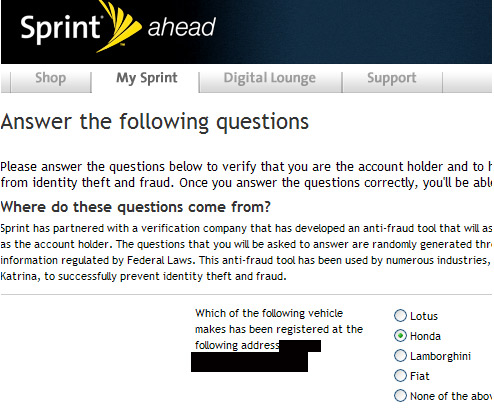
Flawed Security Lets Sprint Accounts Get Easily Hijacked
We found you can hijack a Sprint user’s account as long as you know their cellphone number, just a smidge about them, and have half a brain. Once inside, you have total access to their account. You could change their billing address, order a whole bunch of cellphones sent to a drop location, and leave the victim paying the bill. There’s also the stalker’s wet dream: add GPS tracking to their cellphone and secretly watch their every movement from any computer. Reader Jim told Sprint about this 2 months ago but they ignored him, so I tested it out and am publishing the results in the hope of getting Sprint to fix this exploit. I’ll show you we cracked into a Sprint account and just how much damage I could have done, inside…

Read The Wall Street Journal For Free
Why pay $79 per year to read the Wall Street Journal when you can read it for free? Murdoch’s crown jewel attracts readers by lowering the pay wall for visitors from Google News, Drudge, or Digg. Salon posted step-by-step instructions to help readers exploit this selective generosity.


